Cybercriminals are constantly developing innovative schemes to exploit employees and infiltrate business networks. Thus companies of all sizes req
uire endpoint security services to prevent costly attacks. Cybercriminals often exploit every entry point onto a business network as an entryway into their cyberspace.
Definition
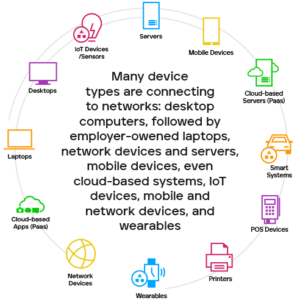
Endpoint security seeks to shield enterprises against threats that target devices connected to their network, such as phones, laptops, desktops, computers, tablets and printers that connect directly. Such devices could include mobile phones, laptops, desktops, computers, tablets, printers, POS (Point of Sale) systems, industrial control systems, IoT sensors etc. In the past, businesses relied upon firewalls as protection from cyberattacks, but with modern remote work policies, BYOD policies, and cloud deployments blurring the distinction between work assets and personal devices, making networks even more susceptible than before – leaving enterprise networks more open compared to attacks from both sides.
Modern endpoint protection solutions come equipped with sophisticated tools such as machine learning, virtual private networks (VPNs), cloud deployments (deployments), encryption and granular application control (GAC). These tools scan and analyze multiple layers of corporate environments to detect vulnerabilities that pose cybersecurity threats and stop attacks as quickly as possible. They also use data on current attacks to predict future ones to protect organizations from unknown malware attacks and zero-day exploits.
Endpoint security encompasses various attacks, such as ransomware (which locks victims’ computers until a ransom is paid), phishing and social engineering (which lure victims into downloading malicious software or clicking dangerous attachments), etc. To counter such threats, endpoint security deploys local device-level analysis and interpretation before placing suspicious activity into a sandbox until an administrator can review and eliminate them.
Scope
An endpoint security solution provides all operational ends of a network with protection, monitoring their activity to detect and respond to potential threats. It’s an invaluable way to prevent data breaches and enhance business security; most attacks come through networks, thus, an efficient endpoint security system can ensure all corners of their operation remain protected.
An effective endpoint security solution can protect companies against malware, ransomware and phishing attacks, safeguard data integrity, and boost productivity. A hacking incident could cost companies financially and time lost due to downtime and reputation damage.
Endpoint security solutions encompass many technologies and tools, such as antivirus software, patch management and privileged access control. A modern endpoint security solution should provide superior protection from cyber threats and attacks; be capable of quickly responding to them so as not to impact performance negatively; be able to detect them before any harm comes to the system’s performance; detect and respond swiftly in case any exist.
Many modern cyber attacks focus on exploiting vulnerabilities at individual endpoints to gain entry to an environment and potentially spread laterally. Therefore, organizations must have visibility and a comprehensive understanding of all active devices within their environment- whether company-owned or BYOD- to stay secure against potential cyber threats.
Benefits
Since employees increasingly work remotely, businesses must secure their assets – such as remote computers and mobile devices – against cybercriminals. An unsecured endpoint could serve as an entryway for attackers to steal sensitive data, breach corporate networks and harm business operations or brand reputation.
One solution is installing an endpoint protection platform (EPP). EPPs are designed to stop malware and other threats from running on endpoint computers while protecting against ransomware attacks or phishing schemes that target endpoint machines.
Many traditional EPPs rely on network firewall technology, which filters data between networks and blocks malicious traffic from entering a business’ computer system. However, such solutions are essential but not enough to protect against today’s sophisticated cyberattacks.
EPPs can detect and block malware, spyware and other attacks that target an endpoint machine. Furthermore, EPPs automatically elevate privileges based on policies, making it harder for attackers to gain entry to sensitive information or systems.
Modern EPPs leverage big data and predictive analytics to identify unknown threats, analyze current attack patterns, and predict future ones. While legacy EPPs were reactive and only searched for known attack methods, predictive analytics can help businesses prevent attacks before they occur.
Implementation
Endpoint security (or endpoint protection) is used to defend corporate networks against threats from remote devices like laptops, mobile phones and desktop computers. Such devices serve as entryways into networks which hackers could exploit to pose serious security threats and vulnerabilities.
Administrators with access to an endpoint security solution typically have antivirus software that scans devices for malware or viruses. A network control component also tracks, monitors and filters inbound traffic to prevent potential attacks on servers and networks. In some solutions, an additional sandbox environment tests applications for suspicious code before it enters an organization’s servers or networks.
Threat detection and response technology (EDR, also referred to as endpoint detection and response) is another component of endpoint security that detects online attacks on end-user devices. EDR software monitors activity on each end-user device in real-time to identify suspicious activities that might indicate an attack has occurred or is ongoing, notifying administrators about such activity and offering suggestions on what steps can be taken next.
Modern endpoint protection solutions also use big data and predictive analytics to enhance performance and scalability, using cloud-based databases to store threat intelligence instead of updating local versions of antimalware or firewall software with information regarding new variants of malware or hacker techniques.
