Attackers aim to breach your defenses. EDR tools can record and store raw telemetry, helping your team identify and respond to threats that pass your perimeter protections.
Consider it as the “black box” for your endpoints; data captured during and after an attack can help prevent similar breaches in the future.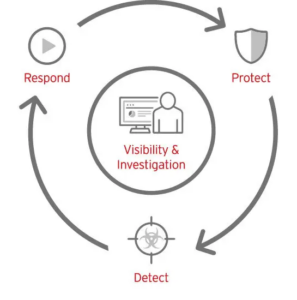
Detecting Threats
EDR solutions monitor endpoints–including employee workstations inside and outside the office, servers, and cloud workloads–to detect suspicious behaviour that could indicate a cyberattack. They use software agents to gather data that will be transmitted back to an on-premises or cloud location for centralized analysis.
Telemetry collected during an investigation is then correlated and analyzed using various security analytics and techniques, including machine learning. This allows the solution to detect patterns of behaviour that serve as indicators of compromise and search for malware files.
Depending on the rules they were predefined for incoming data, an automated response may be initiated, such as logging off specific users or notifying staff. Furthermore, having access to multiple forms of telemetry speeds up investigative efforts.
Once a malicious file is identified, an EDR can investigate further by “sandboxing” or placing it into an environment designed to simulate normal network conditions and observe its behaviours. This allows security analysts to understand better what type of attack has occurred on your system and how it entered. Many EDR solutions integrate with third-party threat intelligence services for improved effectiveness against zero-day attacks or multi-layered exploits; some even feature machine learning/artificial intelligence features to automate investigations by learning your organization’s baseline behaviour and using that to interpret findings more efficiently.
Incident Response
EDR solutions utilize continuous endpoint monitoring to glean security information and analyze it to detect threats. IT professionals can utilize this data to spot attacks even before they begin, quickly shortening response times and mitigating risks.
An EDR solution uses various methods, including machine learning, to evaluate and compare telemetrics from different systems and identify any suspicious activity or potential threats for further investigation. Furthermore, alerts will be generated, and automated responses initiated based on predefined triggers (e.g. isolating an endpoint temporarily to stop malware spreading) can also be initiated automatically by these solutions.
Once a threat has been identified, the system will work to identify its nature and source, providing IT teams with invaluable intelligence that they can use further to bolster future security measures for their organizations. For instance, an EDR solution might reveal that an attack gained entry via circumvention or exploiting weakness in infrastructure.
At its final step, an EDR solution will contain and eliminate threats by blocking malicious processes or deleting infected files, thus minimizing dwell time (when attackers remain undetected within your network), which can damage systems or reduce productivity. It may also provide remediation suggestions to restore functionality to infected systems.
Remediation
Once a threat has breached your perimeter defenses, it must be detected quickly. Early Detection Reporting is one of the key functions of EDR because attackers may lurk undetected until it’s too late.
Once an attack is identified, the next step should prevent it from spreading further. That is where EDR comes into play and is usually part of an endpoint security solution like Duo’s. EDR solutions typically feature antivirus capabilities for protection against known malware. Still, they may also include features like heuristic detection and memory threat prevention that go beyond basic antivirus to identify new exploits and fileless attacks.
Modern EDR tools also feature automated remediation features — such as blocking access to applications if users do not update their devices — that have proven more effective than manual remedies and free up time for your team that could otherwise be dedicated to more productive activities.
Effective data breach protection requires being able to quickly recognize and respond to suspicious activity, so an EDR system should capture images of endpoints at various points over time and automatically reimage or roll back systems once threats have been detected.
Prevention
With enough motivation and time, adversaries will eventually find ways to bypass cybersecurity defenses. EDR solutions are intended to counter this by continuously scanning files for suspicious behaviour and flagging any that appear unsafe.
The solution gathers endpoint telemetry data through agents installed on them or other indirect means and sends it to a central platform for analysis. Here, it filters and correlates this telemetry to discover any anomalous activity that could indicate an attack. It flags it for security analysts for action, such as isolating it from its network connection or remotely wiping and reimagining it to contain infections.
EDR should be understood to be distinct from endpoint protection software (EPP). According to Gartner’s definition of EDR tools, they primarily record endpoint-system level behaviour while monitoring for and responding to incidents as they arise – providing context around any incidents discovered.”
EDR solutions should be combined with EPP, advanced malware detection tools, deception technology, memory exploit prevention and device network firewall to enhance their organization’s cybersecurity posture. As no single product can offer protection from today’s determined attackers, organizations must create a comprehensive security stack with all necessary capabilities to defend against future attacks on their networks.
