EDR vs XDR are security tools designed to detect threats and automate responses. While XDR may seem more sophisticated and comprehensive than EDR, it’s just a repackaged set of tools everyone already utilizes.
Connecting data from disparate security solutions, XDR improves threat visibility and accelerates detection and response to attacks. Furthermore, it improves alerting accuracy by connecting disparate systems.
What Is Extended Detection and Response?
Extended Detection and Response (XDR) is a security technology that safeguards your IT infrastructure. It offers enhanced visibility, rapid threat analysis, and quicker responses when security incidents arise.
XDR provides comprehensive network, endpoint, and cloud protection to stop attackers before they can disrupt your business. It helps keep you ahead of advanced threats like ransomware or fileless malware.
XDR consolidates data and tools to offer consistent visibility across email, endpoints, servers, and cloud workloads for threat detection, analysis, and response. It reduces blind spots, automates remediation tasks, and provides context for quick incident handling.
What Is Endpoint Detection and Response?
Endpoint Detection and Response (EDR) is an innovative technology that continuously monitors security events. EDR tools collect and analyze data from network and endpoint devices for behavioral analysis and automated response using rules-based logic.
EDR (Enterprise Data Retention) is a relatively new technology that is quickly becoming an essential element of enterprise security solutions. It gives enterprises complete visibility into all data flows and potential threats, giving them the edge when dealing with data security breaches.
Comparative to Endpoint Protection Platforms, which only offer device-level visibility, EDR provides real-time endpoint monitoring and analysis.
In addition to detecting suspicious activities, an effective EDR solution should have threat-hunting capabilities and incident triage flow so your security analyst can respond before the threats do more harm. Furthermore, it helps prevent alert fatigue by enabling analysts to prioritize their tasks so they can focus on the most critical events.
Understanding EDR Vs XDR
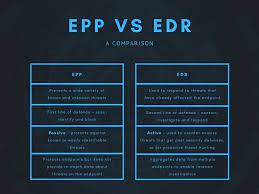
EDR Vs XDR both have their place in cybersecurity, but they also present their own set of challenges. For instance, XDR must work with various sensors and tools, while EDR focuses solely on endpoints and a limited set of solutions.
Security teams often face the daunting challenge of sorting through multiple streams and systems to understand what happened and take appropriate action. An XDR solution takes this task further by automatically correlating and integrating alerts from different sources so analysts have a complete picture.
Security teams can respond to threats by initiating automation targeting specific technologies. For instance, firewall blocks and user password resets might be implemented if malware downloads are detected.
How Do EDR Vs XDR Work?
Traditional security tools, such as EDR and SIEM, have limitations when detecting threats. They rely solely on endpoint telemetry data which is incomplete without context from other security layers like servers, cloud services, identities, and applications.
On the other hand, XDR integrates multiple logical security layers to offer comprehensive visibility into an organization’s entire environment. This comprehensive approach enables XDR systems to detect, investigate and address threats quickly and efficiently.
XDR systems also feature automated root cause analysis to simplify forensic investigations, which can be time-consuming and laborious for security analysts. They offer contextual event data and access to complete datasets, enabling analysts to perform a more profound analysis of an incident and identify its path across emails, endpoints, servers, cloud workloads, and networks.
Comparing EDR Vs XDR Capabilities
While both EDR Vs XDR aim to stop threats, their capabilities differ. XDR provides a more comprehensive solution by protecting, detecting, and responding across multiple data sources.
XDR leverages network, cloud, and third-party data for enhanced threat detection. It also utilizes AI technology to analyze data and detect anomalies.
An XDR platform can also utilize user and entity behavior analytics (UEBA) to detect and respond to zero-day attacks. Furthermore, it adds another layer of analysis over traditional SIEM data, saving security analysts valuable time.
XDR platforms can also significantly improve key SOC performance indicators like mean time to detect (MTTD) and mean time to respond (MTTR), significantly improving threat detection rates and response times.
See Also:
