In networking, an endpoint is any device remotely connecting to a network and exchanging data. This could include desktop computers, laptops, tablets, servers, and IoT (IoT) nodes such as drones or connected homes.
Businesses are increasingly adopting remote work and Bring Your Own Device (BYOD) practices, increasing the number of devices they must manage. As a result, security teams need to become even more efficient and vigilant than before.
A single business may have many individual devices. However, larger companies or businesses with multiple locations must implement a security solution that can centralize the management of all their devices.
Whether you’re a small company or a large enterprise, the threat of cyberattacks can be extremely costly. Breaches have cost organizations millions of dollars in ransomware payments, lost business, and regulatory fines.
What is an endpoint in networking?
An endpoint is a device connected to the network and exchanging data with other devices. It could be anything from a laptop, smartphone, tablet, or desktop computer.
In a networking context, the endpoint is commonly confused with network infrastructure like routers and switches. However, the term IT has an entirely distinct meaning from that of networking infrastructure.
To give employees more flexibility and productivity, companies use endpoint devices in network security and end-user mobility. While these strategies have proved popular, endpoint security presents an increasing challenge as businesses expand their global network footprints and transition towards more mobile working environments.
Why do attackers target endpoints?
In today’s connected world of remote infrastructure and hybrid IT environments, endpoints have become more vulnerable than ever to cyberattacks. Attackers exploit employee device weaknesses to steal data or execute malicious code such as ransomware.
Many attacks also utilize employees’ remote access technologies to gain network access. This gives hackers a convenient entry point into an organization’s system, enabling them to launch attacks against their targets from any location worldwide.
Managing hundreds of endpoints across an organization is a complex task that demands both IT teams’ time and resources. Furthermore, it can be challenging to guarantee each device complies with security policies and has a secure connection to the network.
How does endpoint security work?
Endpoint security shields business systems, customers’ data, and employees’ devices from cyberattacks. It also keeps users’ devices secure against theft and data loss.
Traditional endpoint protection tools and management technologies are employed to safeguard desktops, laptops, tablets, smartphones, servers, and other hardware connected to a network. These solutions utilize centralized consoles, which give system administrators control over the security of corporate endpoints.
Businesses have grown and taken advantage of remote work and bring your own device (BYOD) policies, increasing the number of devices connecting to a corporate network. This has put an additional burden on companies to secure these endpoints.
Why is endpoint security important?
Endpoint security shields users’ devices and businesses from cyber threats. It also ensures that companies keep employees’ data safe, even when they work from home or remotely.
As business environments become more mobile, more devices will be connected to the network and need protection. Thus, IT and security teams must be able to manage devices centralized.
One common way attackers can access enterprise networks is by abusing privileged access on an endpoint. Restricting access and device privileges is the most effective way to protect against this.
What are the benefits of endpoint security?
Endpoint security is a crucial aspect of protecting networks. It safeguards devices, data, and applications against external threats.
As organizations expand, there is an increasing need to secure their networks. To meet this challenge, multi-layered endpoint solutions have been implemented that protect all organizational devices – from traditional desktops to IoT gadgets and mobile phones.
Endpoint security is the primary advantage it provides, protecting data from cybercriminals. This prevents the theft of private information and safeguards sensitive business documents.
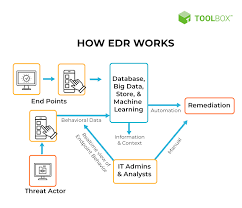
It also helps reduce security costs by providing automated protection to networked servers and workstations and enabling secure access for privileged users. A strong endpoint solution should provide comprehensive cybersecurity measures, including data classification and loss prevention, insider threat monitoring, network and privileged user access control, anti-malware, email gateways, and Endpoint Detection Response (EDR).
See Also:
