Microsoft EDR is an advanced threat defense solution designed to detect and respond quickly to advanced attacks on endpoint devices. As an endpoint security tool, it offers your organization protection against malware attacks or ransomware threats.
This solution boasts an excellent MITRE score and positive user reviews, is affordable and straightforward to deploy; yet some aspects of its ease-of-use and support could use some improvement.
Microsoft EDR Detection
Endpoint devices – like desktop workstations and laptops – play an indispensable part in business operations, while also being prime targets for cybercriminals who seek entry points into corporate networks via these endpoints.
Microsoft EDR detects real-time attacks in real time on endpoint devices and helps you respond promptly by gathering behavioral data such as process information, network activity, kernel and memory usage as well as login activities, registry modifications and file changes.
Threat Intelligence – Third-party partners and Microsoft hunters and security teams provide their threat intelligence to Defender for Endpoint, helping the solution identify attacker techniques and procedures.
Detection engineering is an ongoing cycle in which new detections are devised based on your environment’s intelligence. As such, its success requires an environment conducive to its practice.
A good detection engine should automate the creation of detections using both internal knowledge and threat intelligence from external sources, and can trigger alerts or take actions such as terminating processes or shutting down systems automatically.
Microsoft EDR Prevention
Microsoft EDR is an effective security tool designed to prevent and detect attacks across your organization’s endpoint devices, as well as respond quickly and decisively when threats that could have potentially dire repercussions for your company arise.
Windows 10 EDR technology automatically collects cyber telemetry from endpoints, such as process information, network activity, kernel and memory usage data, login activities, registry changes and file system modifications – this data is then stored for six months so you can gain a full picture of an attack’s origins so as to quickly respond.
By reviewing alerts from an EDR system, human analysts can examine suspicious activities and take appropriate actions to investigate and resolve issues. Once this information has been aggregated into incidents, security teams are better able to understand and address threats effectively.
Microsoft EDR Investigation
An investigation is launched upon receiving alerts on endpoint devices indicating threat signals, gathering behavioral data such as process activity, network activity, kernel and memory usage patterns, login activities, registry modifications and file changes.
Once a threat is identified (such as a user account, email message, URL or file), either automatically by the system or with approval of your security operations team, actions may be taken either automatically or after further discussion with them in your Action center. These resulting actions are listed for your review in this area of our dashboard.
An automated investigation that detects a malicious file submitted by one of your organization users triggers Microsoft for further examination, sending that file for further analysis and showing various attributes about its MD5, VirusTotal detection ratio and Microsoft Defender Antivirus protection if available. The File Details, Incident Details, Malware Detection and File Prevalence cards provide more details regarding each file that was sent for analysis by sending them directly.
An investigation may uncover a volume anomaly, a potential threat surface that indicates an unusually large increase in emails that are similar to those previously received during that same timeframe. This could point to potential vulnerabilities but should not pose serious threats.
Microsoft EDR Response
Endpoint devices have become indispensable tools for remote workers. From laptops, desktops and smartphones, endpoint devices are vital tools in supporting employees working from remote environments by giving access to corporate resources and data as well as critical business applications that support day to day operations. Unfortunately, however, mobile devices such as these are also vulnerable to cyber attacks and exploits – Microsoft Defender for Endpoint takes an aggressive multi-pronged approach in protecting assets and people with next generation threat management, detection and response capabilities.
EDR delivers an optimized security posture that’s both cost-effective and effective, using cutting-edge machine learning algorithms in combination with cloud technology to continuously analyze files to detect anomalies that need immediate action to resolve breaches. In addition, its automated investigation and remediation platform enables your teams to take swift remedial actions on-demand.
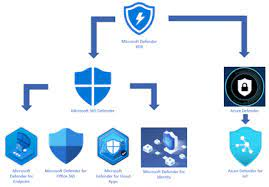
Microsoft provides a full suite of security tools that give you peace of mind that any threats as they emerge are protected against. These include Microsoft’s award-winning malware detection, file protection and endpoint backup/recovery. This gives you peace of mind that threats won’t arise unexpectedly.
